What is the message integrity check MIC within WPA used for
What is the Message Integrity Check (MIC) within WPA used for? Prevent active and passive man-in-the-middle attacks. What is the role of the IEEE in computer networking and wireless communications? To work on developing computer network architecture standards.
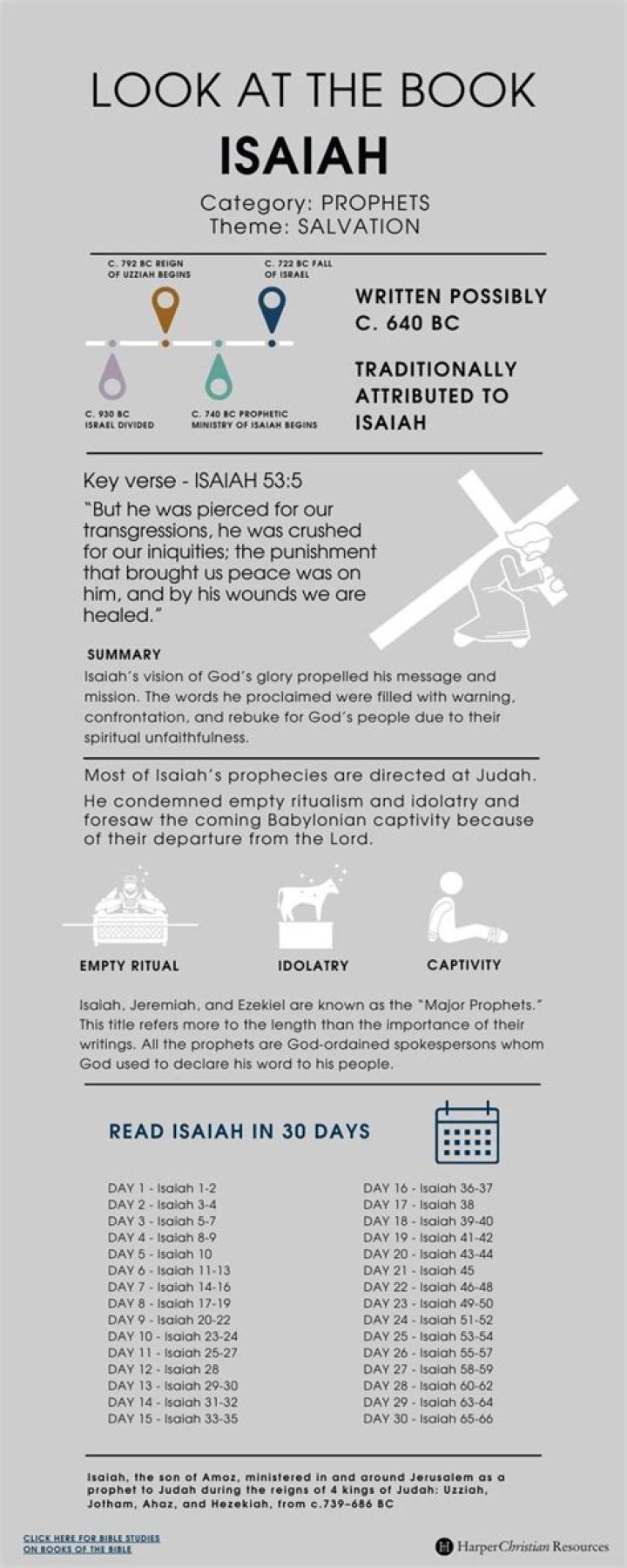
What is the message integrity check MIC?
Enable Message Integrity Check (MIC) – MIC prevents attacks on encrypted packets called bit-flip attacks. During a bit-flip attack, an intruder intercepts an encrypted message, alters it slightly, and retransmits it, and the receiver accepts the retransmitted message as legitimate.
What is MIC failure in WIFI?
This error message is printed when ever a packet with the message header fails the MIC check. This happens very rarely whenever the packets with error get past the MAC level. Also may happen during the transition phase of the encryption key change.
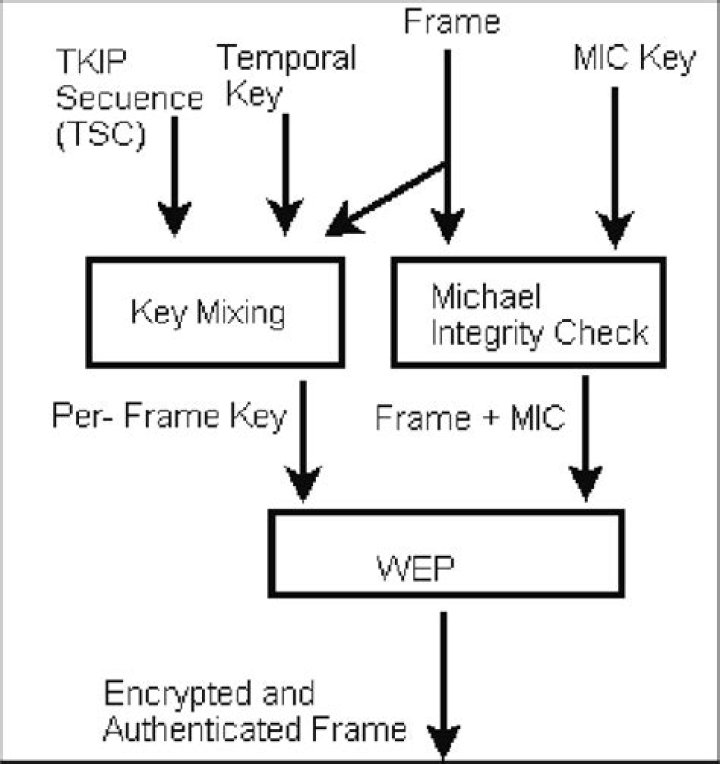
Is Message Integrity Check supported by WPA?
WPA also includes a Message Integrity Check, which is designed to prevent an attacker from altering and resending data packets. … WPA uses a message integrity check algorithm called TKIP to verify the integrity of the packets. TKIP is much stronger than a CRC, but not as strong as the algorithm used in WPA2.What is MIC cryptography?
A message integrity check (MIC), is a security improvement for WEP encryption found on wireless networks. The check helps network administrators avoid attacks that focus on using the bit-flip technique on encrypted network data packets.
What is message integrity?
Browse Encyclopedia Message integrity means that a message has not been tampered with or altered. The most common approach is to use a hash function that combines all the bytes in the message with a secret key and produces a message digest that is difficult to reverse.
What is message confidentiality?
message confidentiality. Two or more hosts communicate securely, typically using encryption. The communication cannot be monitored (sniffed) by untrusted hosts. The communication between trusted parties is confidential. message integrity.
Is TKIP still used?
TKIP was designed by the IEEE 802.11i task group and the Wi-Fi Alliance as an interim solution to replace WEP without requiring the replacement of legacy hardware. … However, TKIP itself is no longer considered secure, and was deprecated in the 2012 revision of the 802.11 standard.What advantage does WPA2 over WPA?
Although WPA is more secure than WEP, WPA2 is more secure than WPA and the right choice for router owners. WPA2 is designed to improve the security of Wi-Fi connections by requiring the use of stronger wireless encryption than WPA requires.
What does TKIP encryption mean?TKIP (Temporal Key Integrity Protocol) is an encryption protocol included as part of the IEEE 802.11i standard for wireless LANs (WLANs). It was designed to provide more secure encryption than the notoriously weak Wired Equivalent Privacy (WEP), the original WLAN security protocol.
Article first time published onHow does the WPA Temporal Key Integrity Protocol encryption technology operate?
While WEP provides each authorized system with the same key, WPA uses the temporal key integrity protocol (TKIP), which dynamically changes the key that the systems use. … This prevents intruders from creating their own encryption key to match the one used by the secure network.
What is Michael MIC failure?
A TKIP MIC failure is when the Michael hash on the received frame does not properly validate. … Michael does have several faults, where the security of the algorithm is less than the actual hash size (64-bits), making it possible to brute-force the MIC in only 2^29 operations.
What is Michael in WPA RSN?
–Message integrity checking is ineffective: WEP message integrity protocol CRC-32 was proved to be ineffective so WPA uses a Message Integrity Check (MIC) mechanism called, ”Michael’.
Why is message integrity needed for network security?
In the world of secured communications, Message Integrity describes the concept of ensuring that data has not been modified in transit. This is typically accomplished with the use of a Hashing algorithm. … The sender will calculate a hash on the message, and include the digest with the message.
How is a message integrity check MIC different from a message authentication code MAC )?
How is a Message Integrity Check (MIC) different from a Message Authentication Code (MAC)? a MIC only hashes the message, while a MAC incorporates a secret key; A MIC can be thought of as just a checksum or hash digest of a message, while a MAC uses a shared secret to generate the checksum.
What is message authentication How is it different from message integrity?
The message authentication code, also referred to as digital authenticator, is employed as an integrity check supported a secret key shared by two parties to authenticate information transmitted between them. it’s supported employing a cryptographic hash or symmetric encryption algorithm.
Can you have message confidentiality without integrity?
Without integrity no system can provide confidentiality. In case of not maintaining the integrity, the existence of the information can be revealed thus compromising the confidentiality. … If there is no integrity, then there is no guarantee of secure operations on that system, which compromises confidentiality.
Does hashing keep messages confidential?
What is Hashing? Whereas encryption algorithms are reversible (with the key) and built to provide confidentiality (some newer ones also providing authenticity), hashing algorithms are irreversible and built to provide integrity in order to certify that a particular piece of data has not been modified.
How data integrity authentication and confidentiality is provided by cryptography?
Cryptography can provide two types of authentication services: Integrity authentication can be used to verify that non-modification has occurred to the data. Source authentication can be used to verify the identity of who created the information, such as the user or system.
Why is message integrity important?
Message Integrity It is very important to ensure that the message that is sent across on the network is staying exactly the same when it arrives at the intended destination. The message can be altered in the transit can be very detrimental, especially when sensitive information is being transferred.
What type of cryptography is used in message integrity?
Symmetric key cryptography is suited for encrypting and decrypting messages, thus providing privacy and confidentiality. The sender can generate a key for each data session to encrypt the message and the receiver can decrypt the message but needs to have the same key for the same session.
Why is message authentication needed?
Message authentication is said to protect the “integrity” of messages, ensuring that each that is received and deemed acceptable is arriving in the same condition that it was sent out—with no bits inserted, missing, or modified.
How secure is WPA Personal?
WiFi Protected Access (WPA) This temporary enhancement still has relatively poor security but is easier to configure. WPA uses Temporal Key Integrity Protocol (TKIP) for more secure encryption than WEP offered.
What Wi-Fi security should I use?
The bottom line: when configuring a router, the best security option is WPA2-AES. Avoid TKIP, WPA and WEP. WPA2-AES also gives you more resistance to a KRACK attack. After selecting WPA2, older routers would then ask if you wanted AES or TKIP.
Is it possible to hack WPS disabled WIFI?
Answer: WPS being disabled does not prevent wifi cracking. Using a good dictionary list with a packet injection wifi adapter can crack even WPA2. … In some situations, the vulnerability even leaves room for an attacker to manipulate data on a Wi-Fi network, or inject new data in.
What does WPA mean on a router?
Wi-Fi Protected Access (WPA) is a security standard for computing devices with wireless internet connections. It was developed by the Wi-Fi Alliance to provide better data encryption and user authentication than Wired Equivalent Privacy (WEP), which was the original Wi-Fi security standard.
Which is better WPA2 AES or TKIP?
In 2006, WPA became a deprecated protocol, and WPA2 replaced it. The notable drop of TKIP encryption in favor of the newer and more secure AES encryption (Advanced Encryption Standard) led to faster and more secure Wi-Fi networks. AES encryption is much stronger in comparison to the stopgap alternative that was TKIP.
Why is TKIP insecure?
According to Cisco, TKIP is vulnerable to packet decryption by an attacker. However, only the authentication key can be stolen by an attacker, not the encryption key.
What does AES and TKIP mean?
TKIP (short for Temporal Key Integrity Protocol) is an encryption method. … AES (short for Advanced Encryption Standard) is the Wi-Fi® authorized strong encryption standard. WPA-PSK/ WPA2-PSK and TKIP or AES use a Pre-Shared Key (PSK) that is 8 or more characters in length, up to a maximum of 63 characters.
Is WPA WPA2 TKIP secure?
WPA/WPA2 (TKIP) is not considered secure. If this is your Wi-Fi network, configure the router to use WPA2 (AES) or WPA3 security type. … Briefly here is a bit of information on the different security protocols for Wi-Fi.
What is WPA-PSK TKIP WPA2-PSK AES Netgear?
By default, the WPA-PSK [TKIP] + WPA2-PSK [AES] radio button is selected so that new or old computers and wireless devices can connect to the WiFi network by using either WPA2 or WPA security. The Passphrase field displays. In the Passphrase field, enter the network key (password) that you want to use.